In today’s digital landscape, securing communication between clients and servers is paramount. SSL/TLS protocols are widely used to encrypt data, ensuring privacy and integrity. However, there are scenarios where decrypting this communication is necessary for various purposes, such as load balancing, security inspection, or performance optimization. This is where reverse proxy comes into play.
What is a Reverse Proxy?
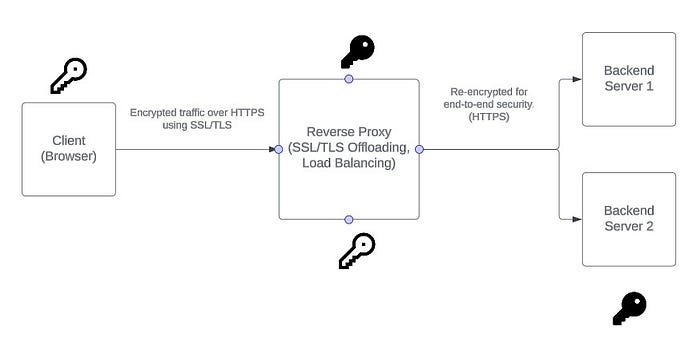
A reverse proxy is a server that sits between client devices and backend servers, forwarding client requests to the appropriate server and returning the server’s response to the client. This setup offers several benefits, including load balancing, caching, and enhanced security.
Decrypting SSL/TLS with a Reverse Proxy
When a reverse proxy is configured to handle SSL/TLS decryption, it acts as an intermediary that terminates the encrypted connection from the client, decrypts the data, and then forwards the unencrypted data to the backend server. This process is known as SSL/TLS termination or offloading.
When using SSL/TLS termination at a reverse proxy, the private key for the SSL/TLS certificate is stored securely on the reverse proxy server itself, with restricted access to prevent unauthorized access or compromise.

Benefits of SSL/TLS Termination
- Performance Optimization: Offloading the SSL/TLS decryption process to the reverse proxy reduces the computational load on backend servers, allowing them to focus on processing application logic.
- Security Inspection: Decrypting traffic at the reverse proxy enables security tools, such as intrusion detection systems (IDS) and web application firewalls (WAF), to inspect the data for threats before it reaches the backend servers.
- Simplified Certificate Management: Managing SSL/TLS certificates on a single reverse proxy server is easier than maintaining them across multiple backend servers.
Implementation Example: Consider an Nginx reverse proxy configured to decrypt SSL/TLS traffic. The proxy receives encrypted requests from clients, decrypts them, and forwards the unencrypted requests to backend servers. Here’s a simplified configuration example:
server {
listen 443 ssl;
server_name example.com;
ssl_certificate /etc/nginx/ssl/example.com.crt;
ssl_certificate_key /etc/nginx/ssl/example.com.key;
location / {
proxy_pass http://backend_server;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
}
}
In this setup, Nginx handles the SSL/TLS decryption and forwards the unencrypted traffic to http://backend_server.
Real-World Use Cases
- Popular video streaming websites like Netflix use NGINX as reverse proxy and load balancer to handle the massive traffic generated by their millions of users. By decrypting SSL/TLS traffic, they can optimize performance and ensure secure delivery of content.
- Companies like Cloudflare employ globally distributed reverse proxy network to protect websites from DDoS attacks and other security threats. Decrypting SSL/TLS traffic allows these companies to inspect and filter malicious requests effectively.
- Payment portals like PayPal and others use reverse proxies to enable scaling while blocking millions of fraudulent transactions per month. SSL/TLS termination helps companies like PayPal inspect and secure transactions efficiently.
Re-encryption for End-to-End Security
In some cases, maintaining encryption between the reverse proxy and the backend servers is necessary. This can be achieved by re-encrypting the traffic before forwarding it, ensuring end-to-end encryption.
The benefits of end-to-end encryption include enhanced security, as it ensures that data remains encrypted throughout its journey, protecting it from potential interception or tampering. It also helps meet regulatory requirements for data protection and privacy by maintaining encryption across all communication channels.
However, there are challenges as well to consider, such as increased complexity, which requires additional configuration and management of SSL/TLS certificates for both the reverse proxy and backend servers. Additionally, re-encrypting traffic can introduce performance overhead, adding latency and computational load that may impact performance.
Potential Security Risks of using reverse proxies
- Exposure of Sensitive Information: Reverse proxies might expose sensitive information through headers, leading to potential security vulnerabilities. Proper configuration and header management are crucial to mitigate this risk.
- Insecure Configurations: Misconfigurations of reverse proxies can introduce security risks. It’s essential to follow best practices for configuration, including regular audits and assessments to identify and rectify potential vulnerabilities.
- Amplification Attacks: While reverse proxies protect against DDoS attacks, misconfigurations can lead to amplification attacks, where attackers exploit the proxy to amplify the volume of traffic directed at the target.
Final Thoughts
Reverse proxies play a crucial role in SSL/TLS communication, offering performance optimization, enhanced security, and simplified certificate management. By terminating SSL/TLS at the proxy, organizations can efficiently manage encrypted traffic and ensure secure, high-performance communication between clients and servers. However, it is vital to be aware of potential security risks and implement best practices to maintain a secure and robust infrastructure. Additionally, implementing end-to-end encryption between the reverse proxy and backend servers can further enhance security, despite the added complexity and performance overhead.
Leave a comment